Before Trust Over IP Foundation, trust architects had a vision.
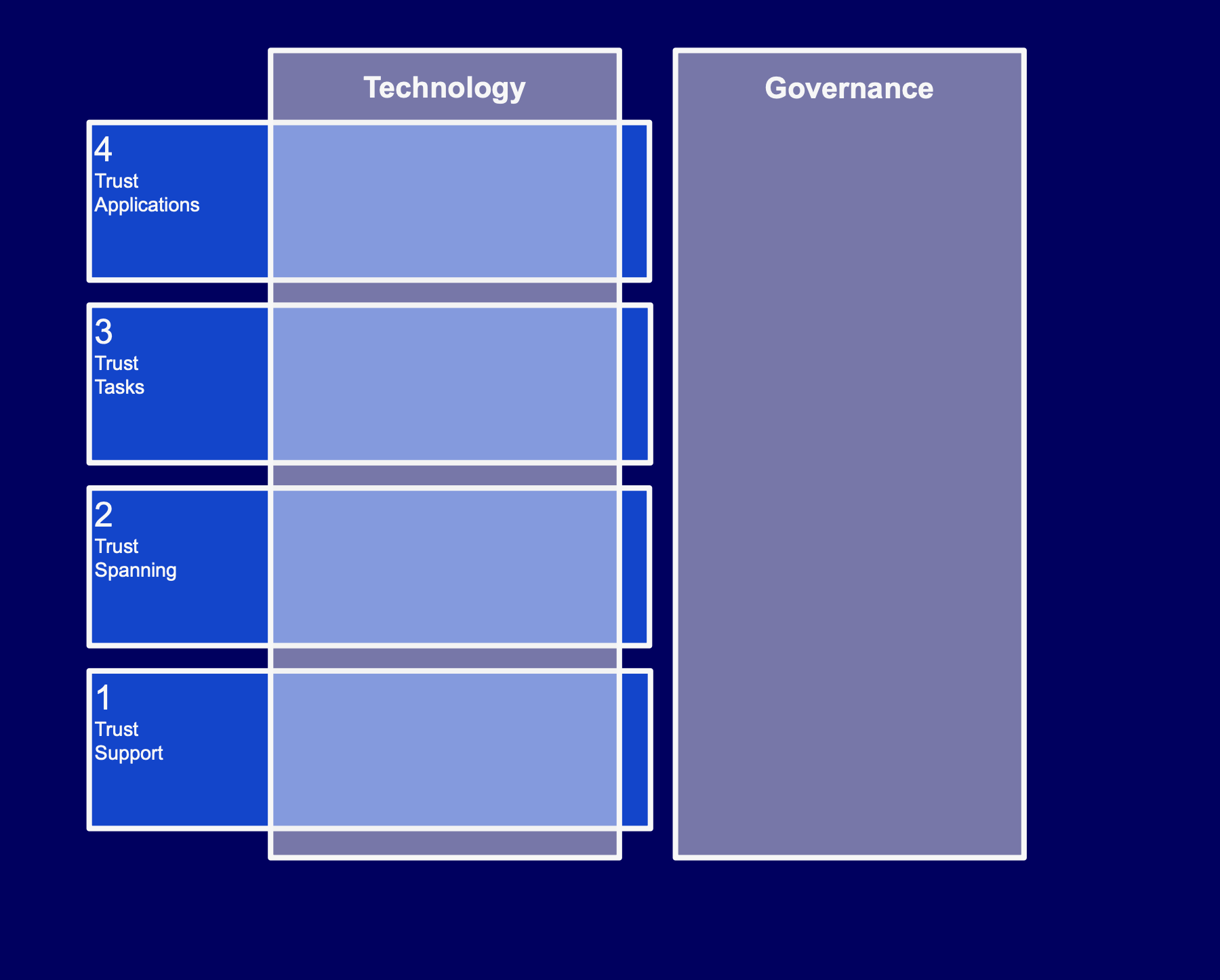
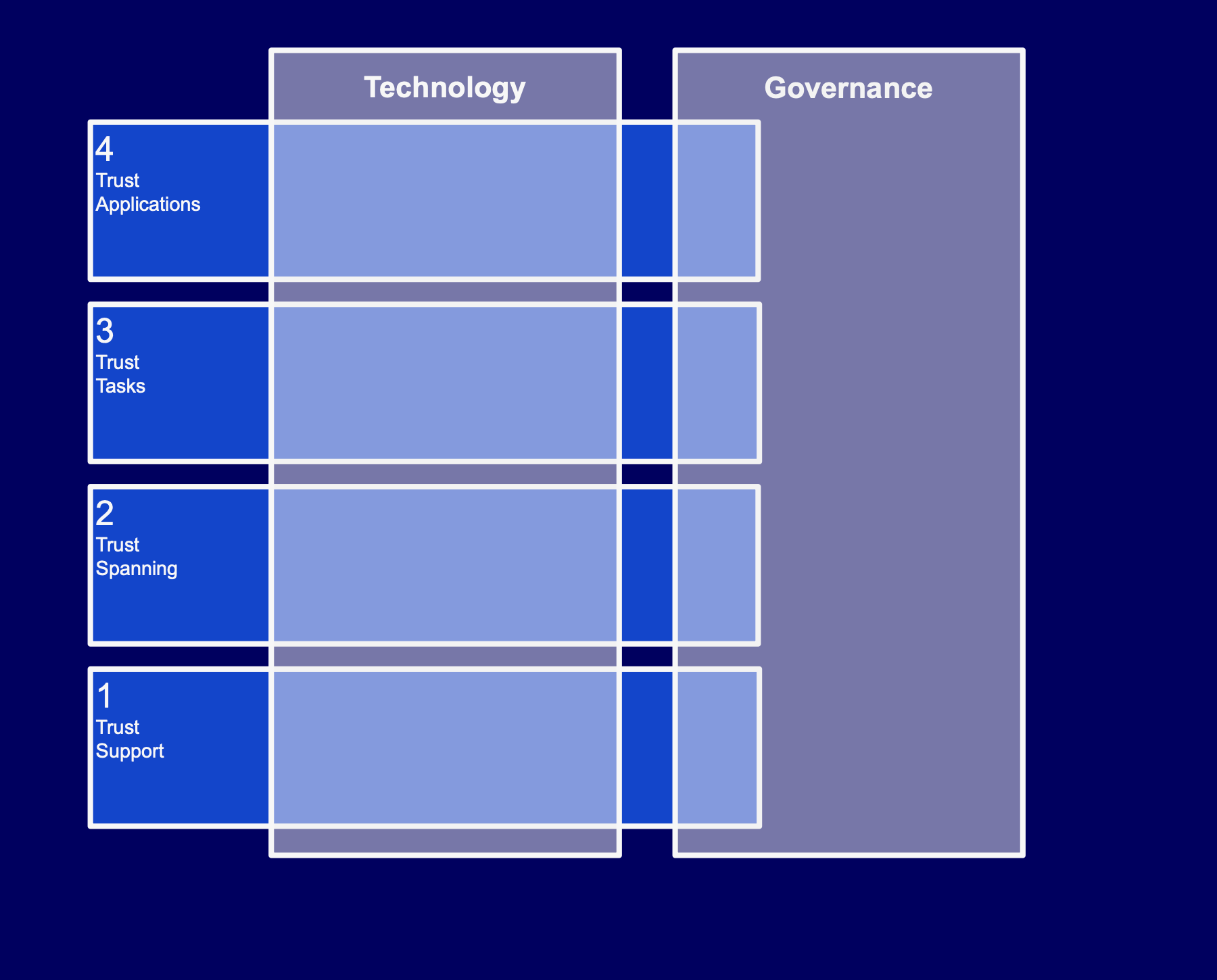
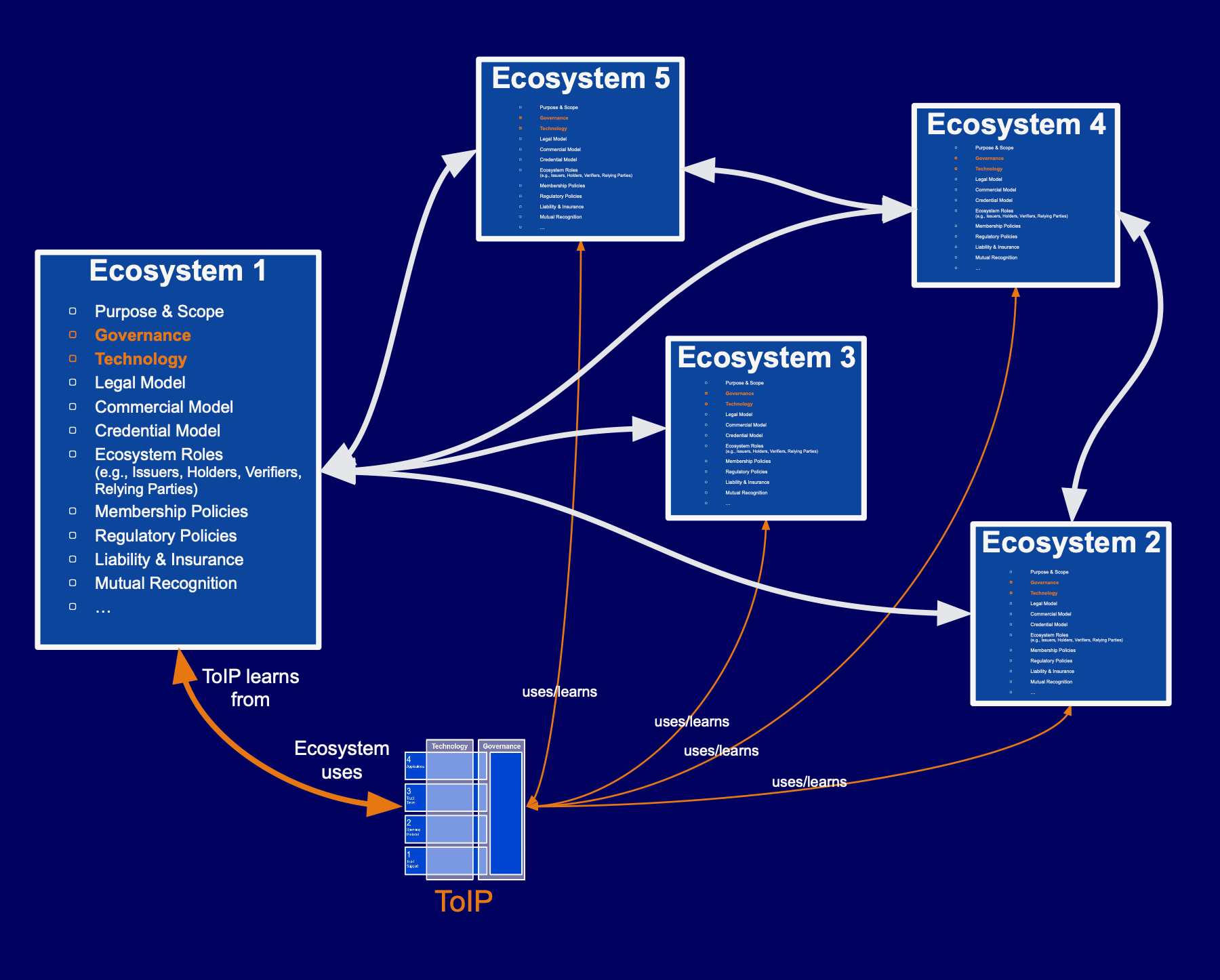
There would be a “trust layer” for the Internet, achieved by following the same architecture as the Internet.
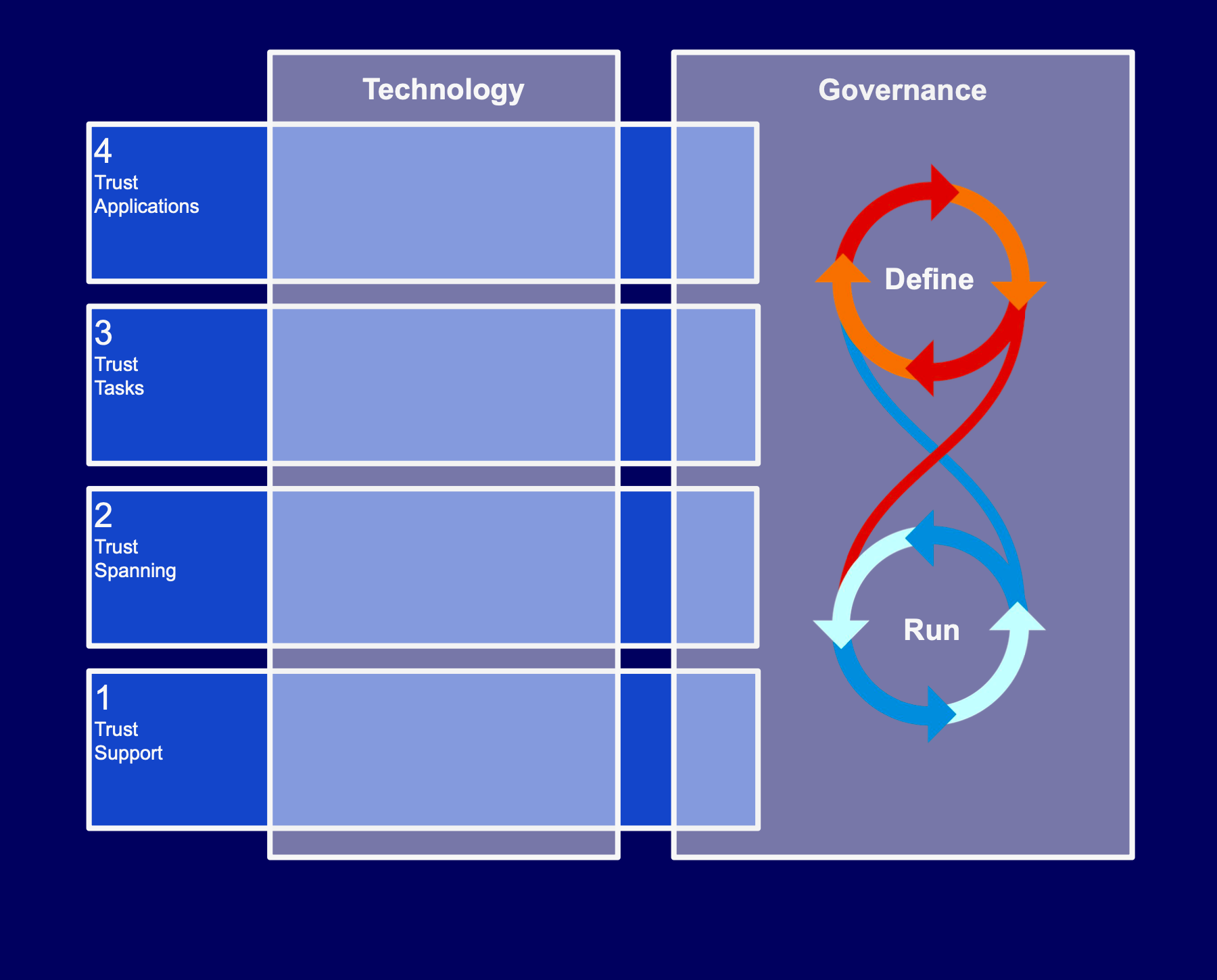
Each peer would be an instance of a standard “stack” of protocols, just as each device on the Internet runs an instance of the TCP/IP stack.
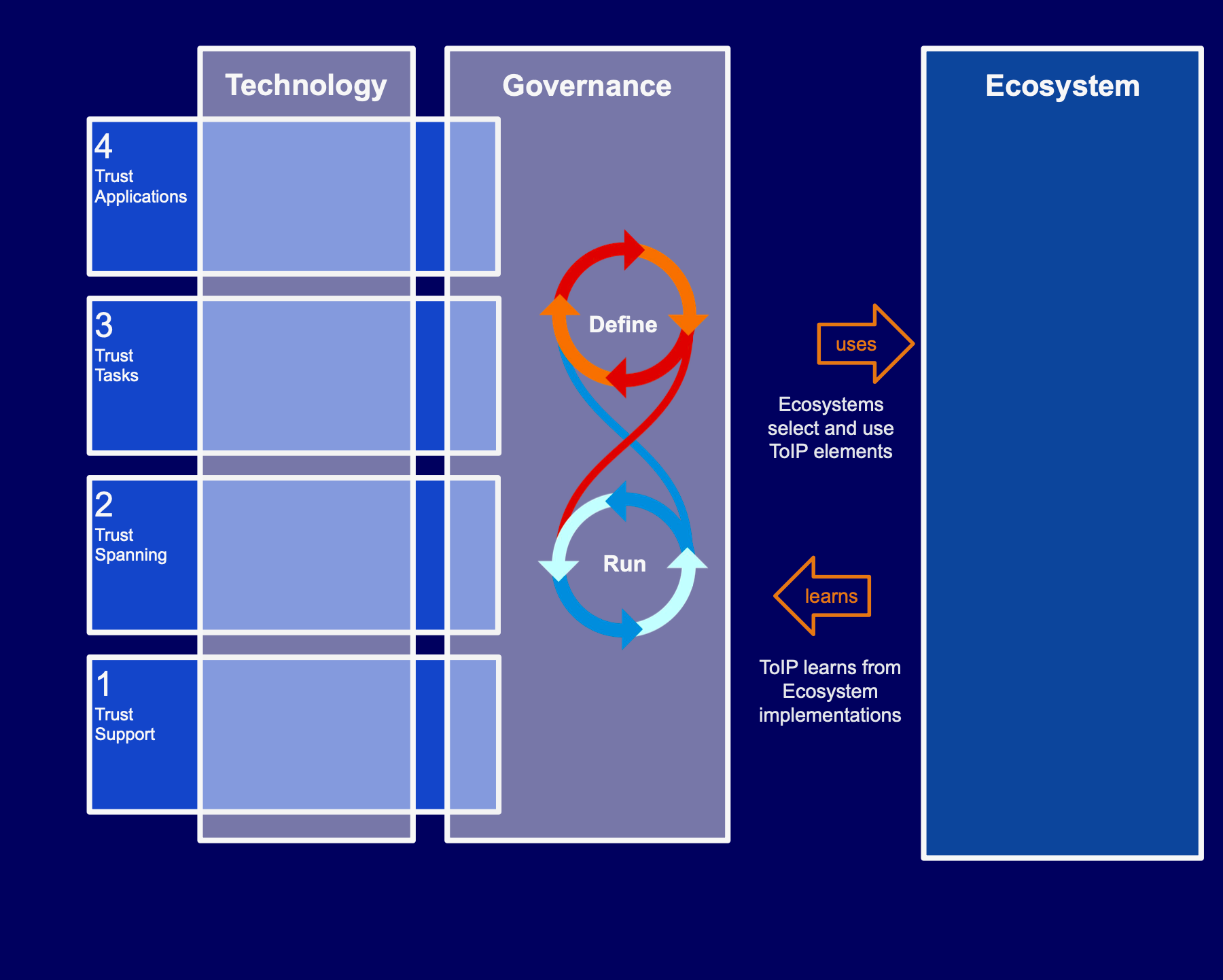
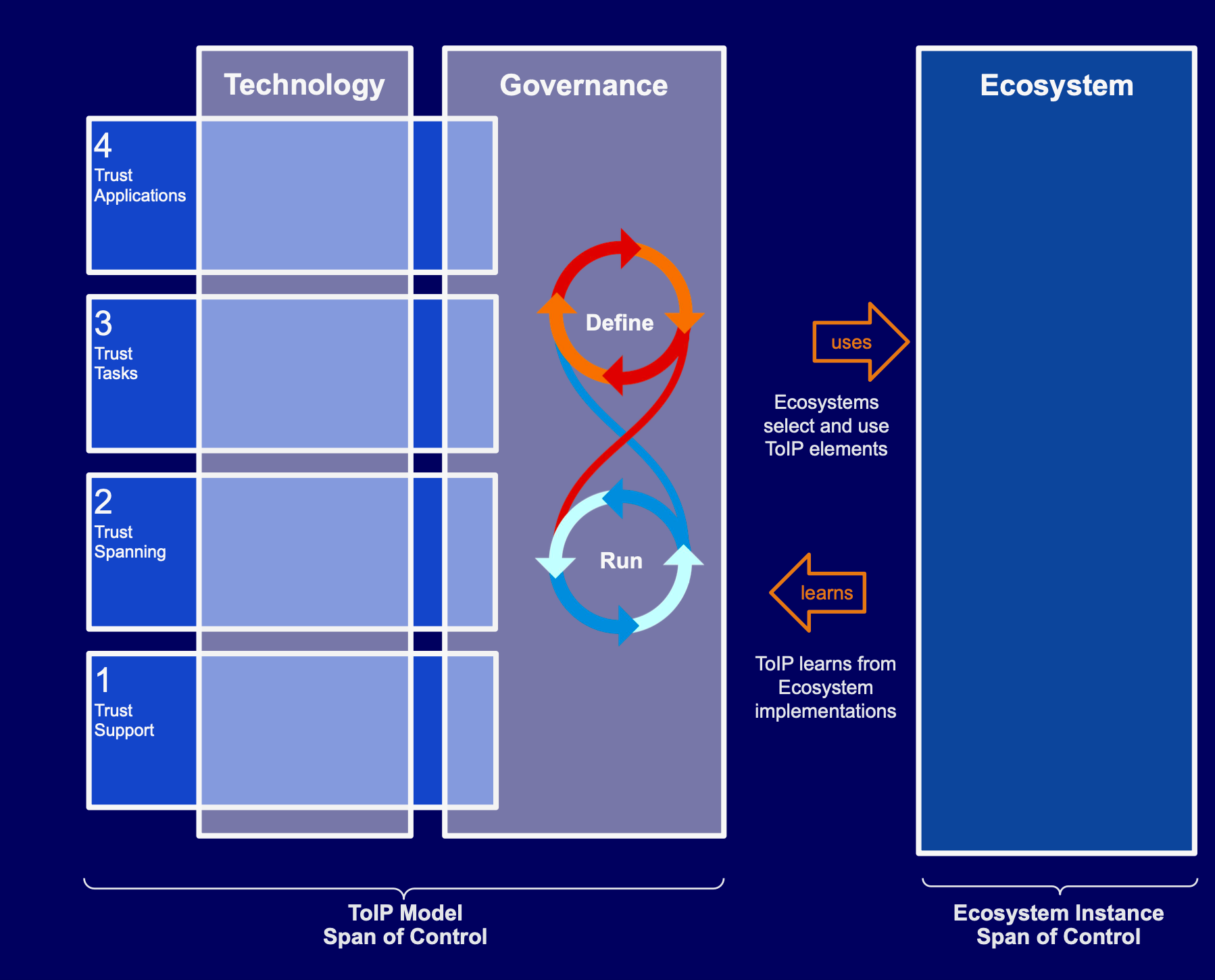
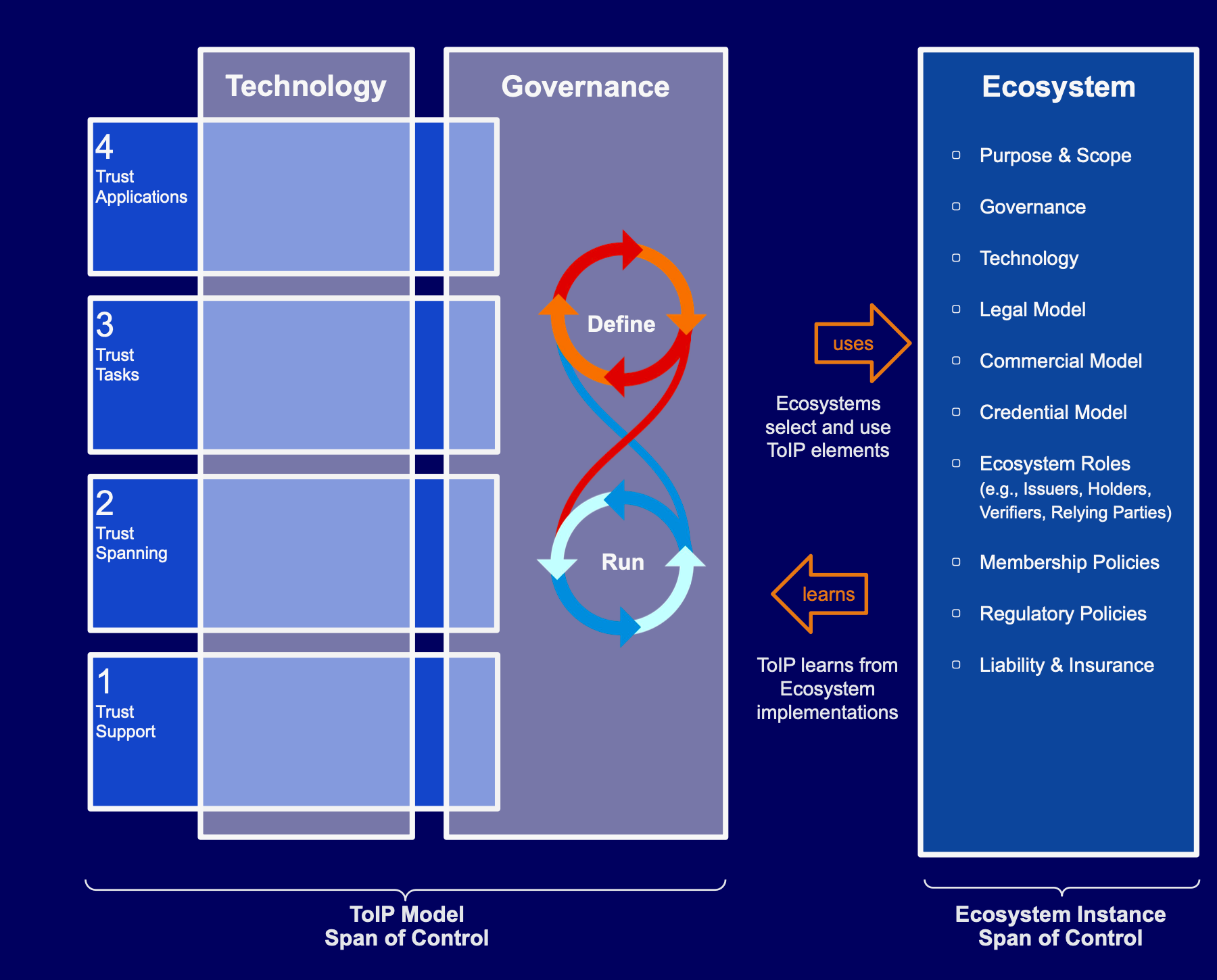
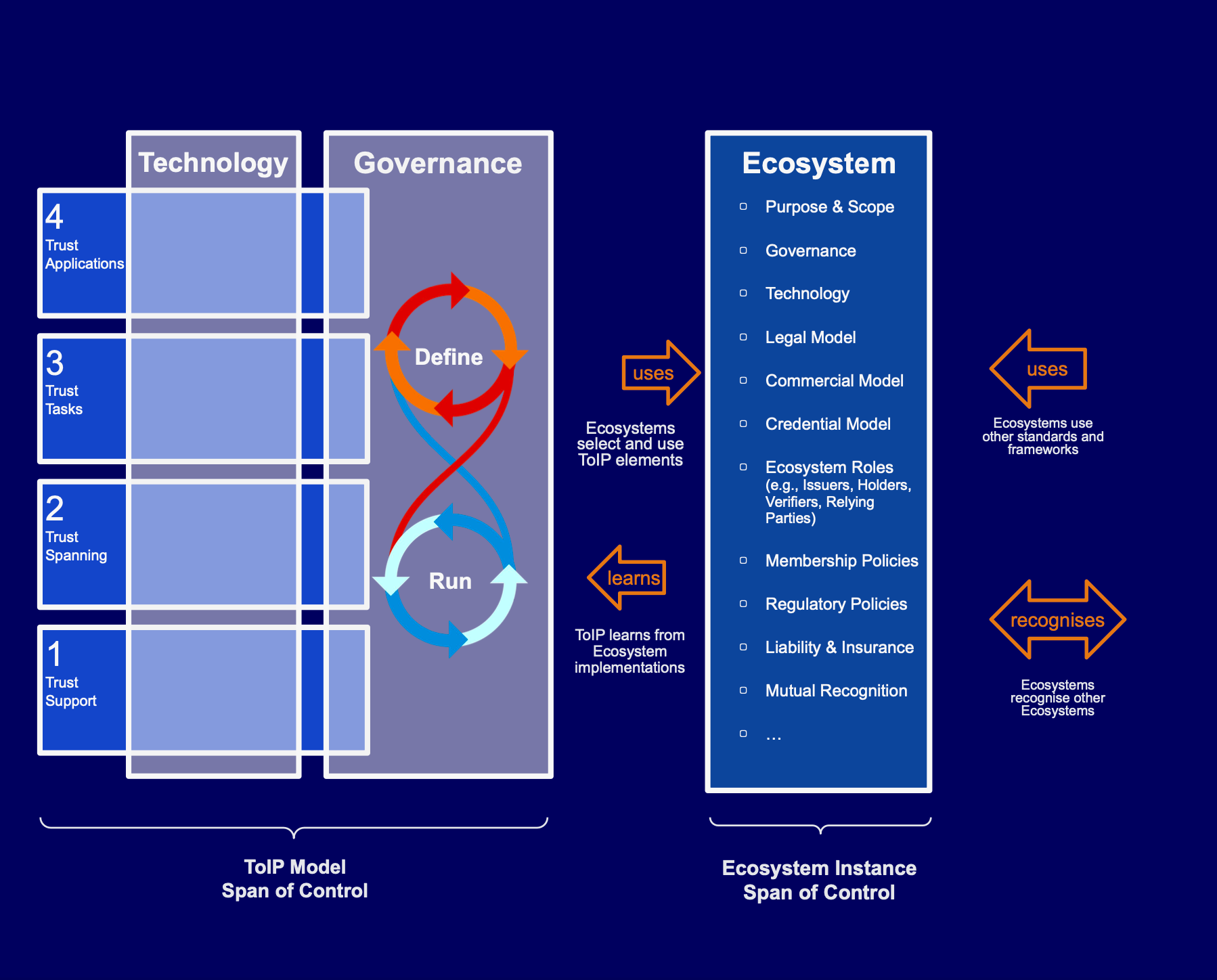
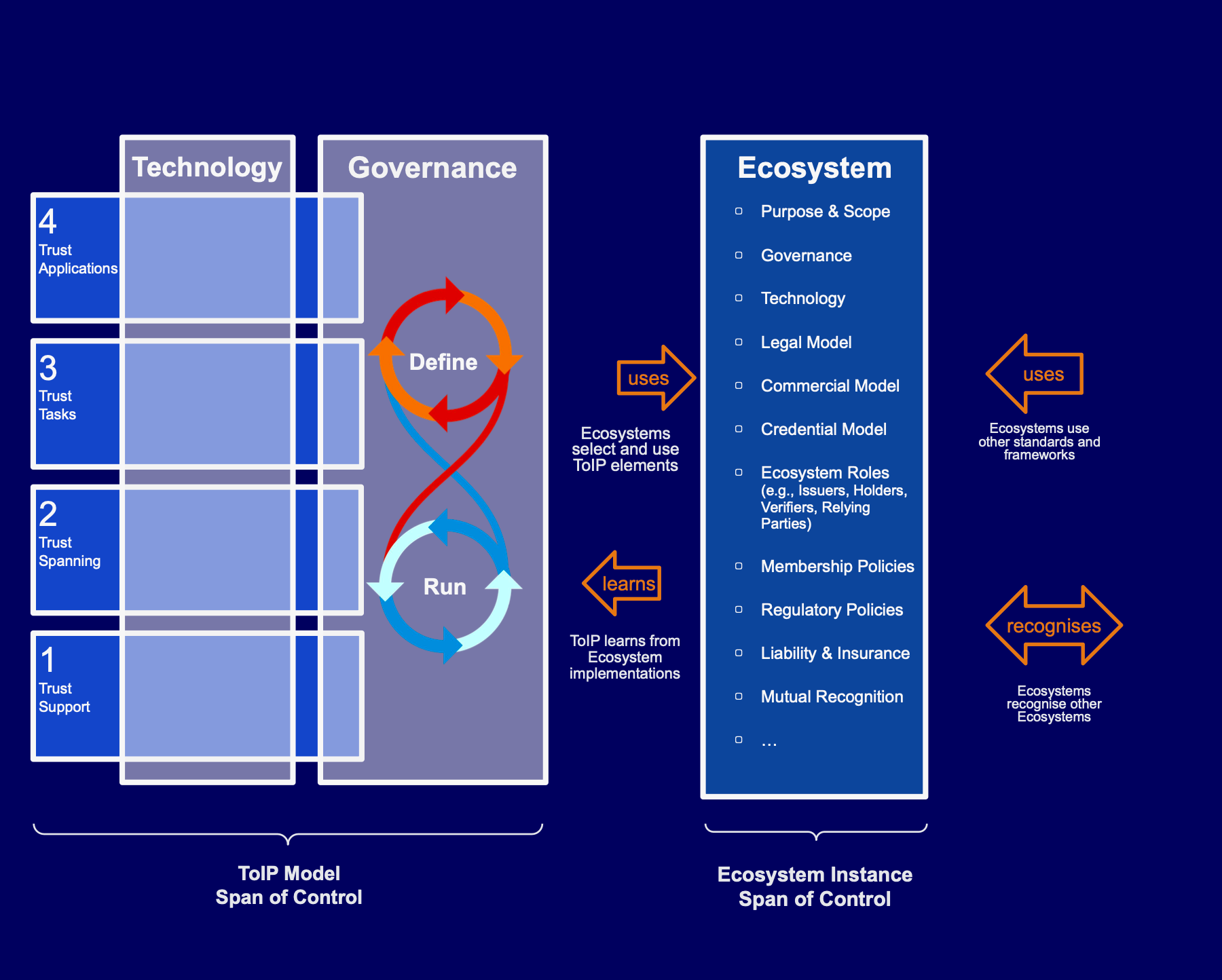
Today, that vision, with its combination of technology, governance and ecosystems, is seen in the journey below to what we call the Trust Over IP Model.
Here’s our story.